Edit Vpn Connection
To edit a VPN Connection, please follow the instructions below:
Step 1: From the menu, select Network , then go to the VPN Site-to-Site tab. Here you can manage all existing VPN Connections. Select Edit VPN Connection. 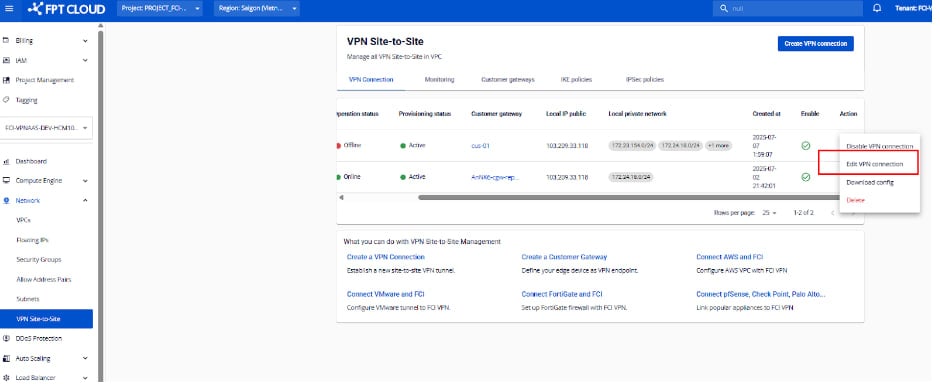 Step 2: Edit the configuration details to update the VPN Connection. The VPN Connection parameters are divided into three main sections:
Step 2: Edit the configuration details to update the VPN Connection. The VPN Connection parameters are divided into three main sections:
- General Information (contains basic connection details)
- Remote VPN Information (contains encryption and customer-side details)
- Dead Peer Detection (defines retry settings when connection issues occur)
Section 1: General Information 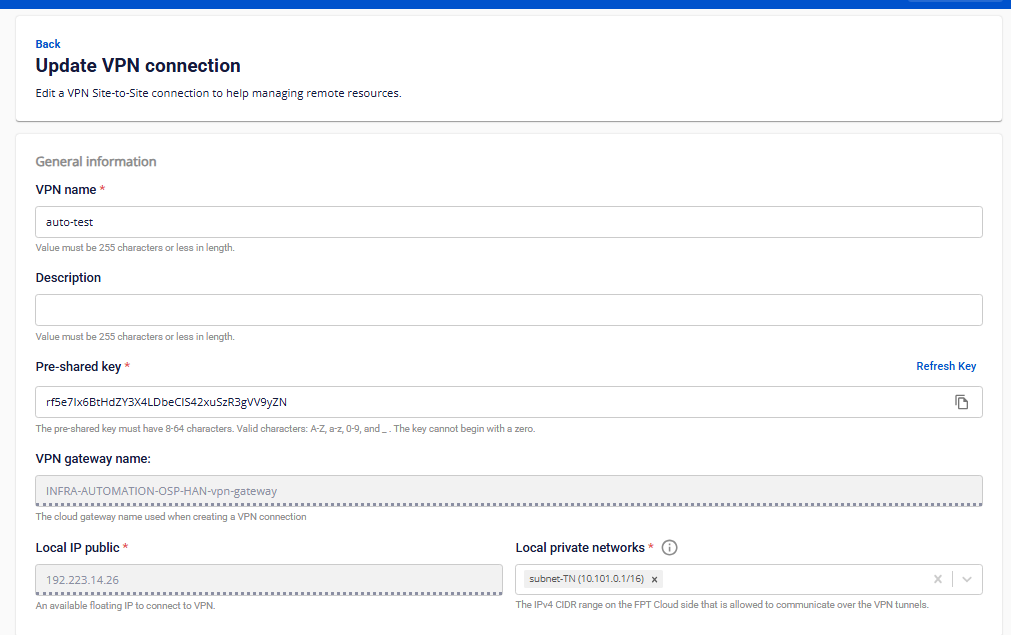
| Field | Description |
|---|---|
| VPN name | Name of the VPN Connection. |
| Description | Description of the VPN Connection. |
| Pre-shared key | The shared security key between the two devices. |
Users can generate a new key by clicking Refresh Key , and copy it by clicking Copy. |
| Local IP public | Public IP address assigned by the FPT Cloud system. |
| Local private networks | The private network range of your resources within FPT Cloud. |
Section 2: Remote VPN Information 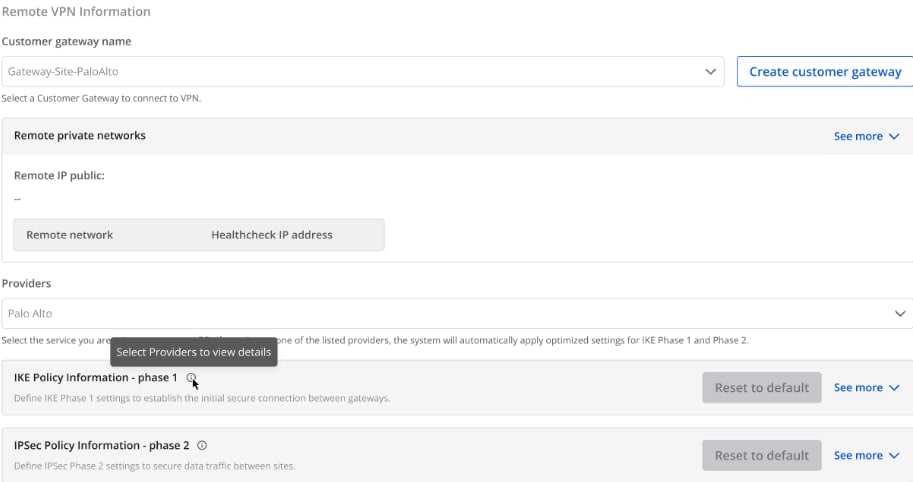 Customer gateway
Customer gateway
| Field | Description |
|---|---|
| Customer gateway | |
| Customer gateway | Configuration information of the remote endpoint. At this step, select the correct Customer Gateway you want to connect to. |
If you don’t have a Customer Gateway yet, please click here for setup instructions. |
| Providers | List of VPN service providers supported by FCI. |
| IKE Policy | |
| Authorization algorithm | The algorithm used to authenticate data during VPN setup.
Available values: sha1, sha256, sha384, sha512, aes-xcbc
Recommended value: sha256 for a balance between security and performance. |
| Encryption algorithm | Algorithm used to encrypt the security key exchange process.
Available values: aes-128, aes-192, aes-256, aes-128-gcm-8, aes-128-gcm-12, aes-128-gcm-16, aes-192-gcm-8, aes-192-gcm-12, aes-192-gcm-16, aes-256-gcm-8, aes-256-gcm-12, aes-256-gcm-16.
FCI recommends using aes-128-gcm-12 for an optimal balance between security and performance. |
| IKE version | Supported IKE protocol versions.
Values: ikev1, ikev2 |
| Lifetime units | The time unit for IKE connection lifetime.
Default: second |
| Lifetime value | The specific lifetime value for Phase 1. |
| DH Group | Diffie-Hellman group used for generating initial key exchange.
Values: group_1, group_2, group_5, group_14, group_15, group_16, group_17, group_18, group_19, group_20, group_21. |
| Phase 1 negotiation mode | Defines how both devices establish the secure channel in IKE Phase 1.
Values: main, aggressive (default: main). |
| IPSec Policy | |
| Authorization algorithm | Algorithm used to authenticate data during VPN operation.
Values: sha1, sha256, sha384, sha512, aes-xcbc.
Recommended: sha256 for balance between security and performance. |
| Encapsulation mode | The mode for encrypting and encapsulating transmitted data.
Default: tunnel. |
| Encryption algorithm | Algorithm used to encrypt the actual VPN traffic.
Values: aes-128, aes-192, aes-256.
Recommended:aes-256 for balance between security and performance. |
| Lifetime units | Default: second |
| Lifetime value | Duration of an IPSec session before re-establishment. |
| Perfect forward secrecy | Option ensuring session key security (PFS, usually paired with DH Group).
Values: off, group_1, group_2, group_5, group_14, group_15, group_16, group_17, group_18, group_19, group_20, group_21.
Recommended: group_14 for a balanced security level. |
| Transform protocol | Protocol defining how encryption and authentication are applied in IPSec.
Values: esp, ah |
Provider
- FCI currently supports pre-configured settings for the following providers: AWS, Fortigate, Palo Alto. For optimal connectivity, FCI recommends using these configurations.
- For other providers not listed above, please enter the IKE and IPSec parameters manually as instructed in the sections above.
Default configuration parameters for supported providers: